What is Infostealer.Fightpos?
Infostealer.Fightpos is a dangerous and harmful Trojan virus. It is created by those bad guys who aim to collect the computer users’ information to play vicious actions, which may be a big threat to the security and privacy. Once installed on the target computer, it will open a backdoor on the infected device, which may introduce other computer threats into the machine. Besides, the computer users may encounter many other computer problems such as slow running speed, unstable Internet connection, crashing, blue screen, etc. All in all, this Trojan virus is very malicious, which can mess up your computer system.

How Does Infostealer.Fightpos Distribute?
The same as other Trojan viruses, Infostealer.Fightpos can penetrate into the computer system without being noticed through many different ways. It is able to get into the computer through freeware, shareware, strange links, peer-to-peer files or files from strangers, etc. In addition, this Trojan virus also is distributed via some corrupted websites because cyber criminals usually distribute various malware into those websites. Once users open those corrupted websites by accident or click on something from them, this Trojan horse or other computer viruses will catch the chance to install itself on user's’ computer system secretly. Besides, this Trojan virus also can sneak into the computer system via spam email attachments which may contain attractive messages or other things luring the users to open them.
How to Prevent Your PC From Infostealer.Fightpos?
To safeguard your PC from Infostealer.Fightpos, the computer users should pay attention to the online activities especially the download and installation of freeware and shareware, etc because most potentially unwanted programs usually is bundled with the installation of free software from unsafe sources. What is more, the computer users should not visit corrupted websites or malicious contents when surfing on the Internet. Besides, users should not open email attachments especially those from strangers easily unless you ensure that they are safe.
Necessary to Remove Infostealer.Fightpos
Infostealer.Fightpos is really dangerous and harmful. Once installed, it will do much harm to the computer system. It can create many junk files in the system everywhere. Besides, it will change the computer’s important settings such as start-up items, registry entries, etc. As you see, this Trojan virus is a big danger to the computer users, so, it should be removed without any delay.
>>Solution 1: Remove this trojan virus by following a similar video guide
>>Solution 2: Remove this trojan virus with step-by-step manual removal guides
>>Solution 3: Remove this trojan virus automatically with SpyHunter
Solution 1: Remove Infostealer.Fightpos by Following a Similar Video Guide
Solution 2: Remove Infostealer.Fightpos with Step-by-Step Manual Removal Guides
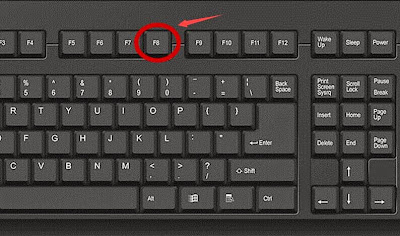
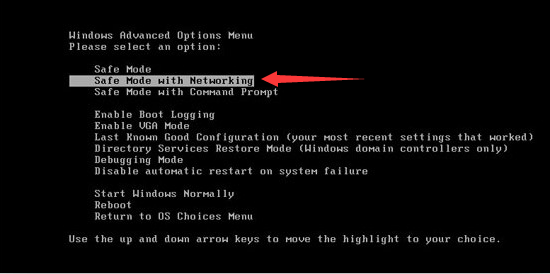
Turn the PC on and press the key F8 on the keyboard repeatedly as soon as you see anything on the screen until the screen. That is to say, when you enter Windows’ Safe Mode, please choose the option “Safe Mode with Networking”. Then hit Enter on the keyboard. System will be loading files into this mode afterward.
>>Step2: End all the harmful running processes related to Infostealer.Fightpos
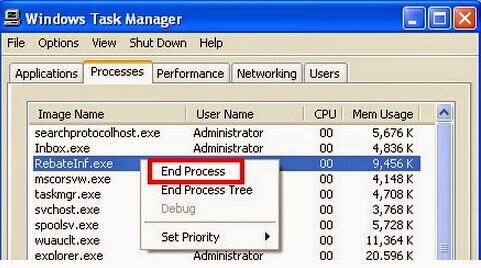
For Windows XP Users:
1. Press Ctrl+Alt+Del keys on the keyboard at the same time to open Windows Task Manager
2. Under the tab Processes, find out and right click on all the processes associated with this trojan virus, then click End Process
1. Click on Task Bar , then select Start Task Manager to open Windows Task Manager (or Press Alt+Ctrl+Del keys at the same time to open Windows Task Manager.)
2. Under the tab Processes, find out and click on all the processes related to the trojan virus, then click End Process
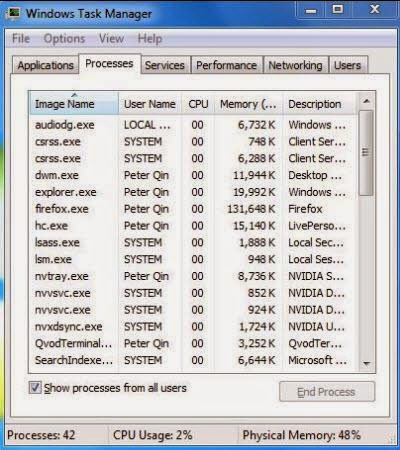
1. Click on the Task Bar, then select Task Manager
2. Under the tab Processes, find out and click on all the processes related to the this trojan virus, then click End Process
>>Step3: Show and clean all hidden files related to Infostealer.Fightpos
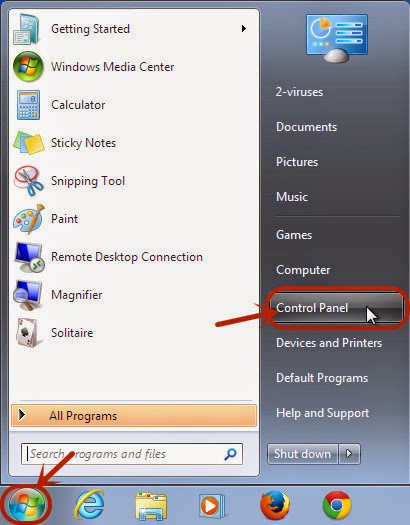
1. Click the Start button and choose Control Panel;
1. Click the Start button and choose Control Panel;
2. Click Appearance and Personalization, then find Folder Options and double-click on it.
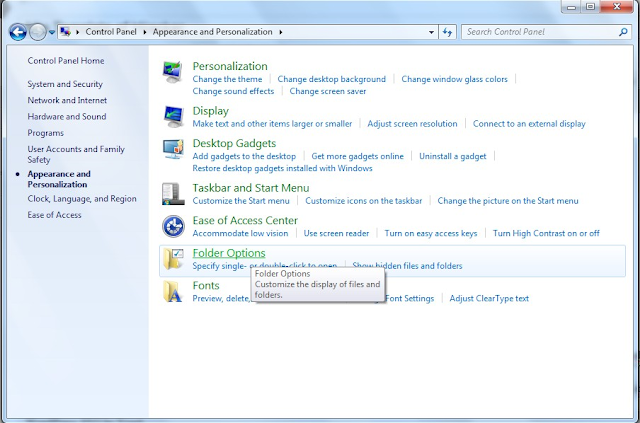
3. In the pop-up dialog box, click the View tab and uncheck Hide protected operating system files and click OK button.

%CommonAppData%\<random>.exe
C:\Windows\Temp\<random>.exe
%temp%\<random>.exe
C:\Program Files\<random>
>>Step4: Remove all the malicious registry entries of Infostealer.Fightpos
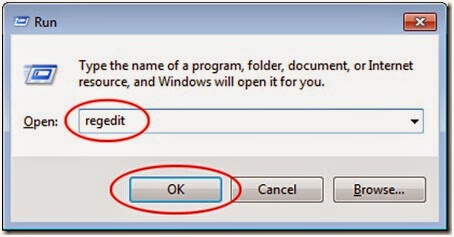
Press Win+R together on the keyboard to open Run box, then type Regedit into the search blank and pressing OK. Then, the Registry Editor window will pop up. And then, delete all registry entries associated with this trojan virus
Press Win+R together on the keyboard to open Run box, then type Regedit into the search blank and pressing OK. Then, the Registry Editor window will pop up. And then, delete all registry entries associated with this trojan virus
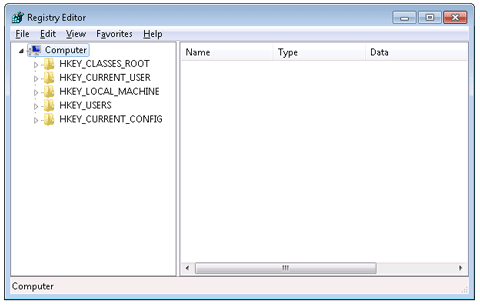
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\MpCmdRun.exe
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\MpUXSrv.exe
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\MSASCui.exe
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\msconfig.exe
Note: As you can see, manual removal is a complicated process which usually requires enough professional computer knowledge and time to complete. For inexperienced computer users, a minor mistake during this process may result in data loss even system damage. So, if you are inexperienced in manual removal, you are suggested to use a reputable and powerful anti-spyware application like SpyHunter to help you remove Infostealer.Fightpos effectively and for good.
Solution 3: Automatically Remove Infostealer.Fightpos with SpyHunter
If you have difficulties in removing Infostealer.Fightpos manually, you are suggested to use SpyHunter to help you remove this trojan virus completely and for good. SpyHunter is a powerful, real-time anti-spyware application which can deliver ongoing protection against the latest malware, trojans, rootkits and malicious software. The following steps are helpful for you to download and install SpyHunter to remove this trojan virus effectively, which will save your time as well as energy.
Step1: Click the icon “Download”. When you click the link, you can see the next step as following step2.
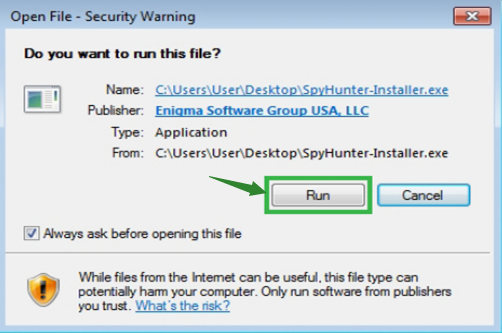.png)
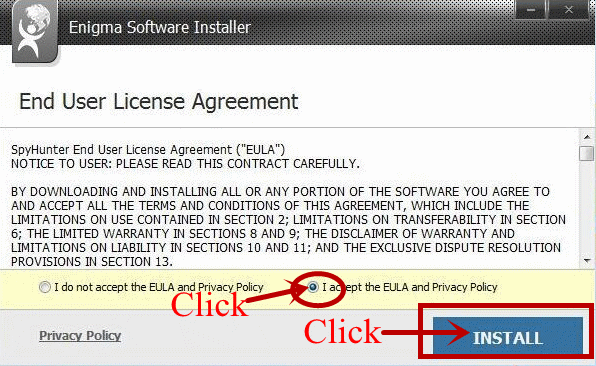
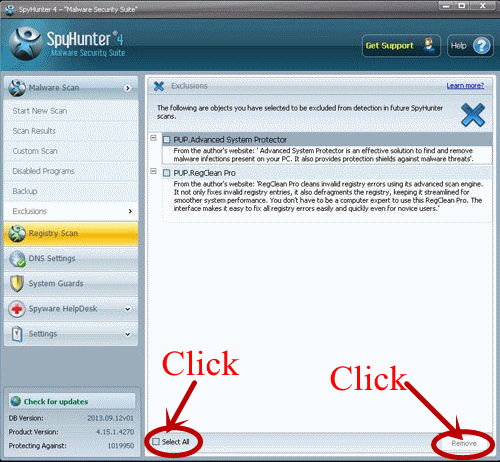
Step3: Please choose the option “I accept the EULA and Privacy Policy”, and then click the button “INSTALL”. When the SpyHunter is set up successfully on your desktop, you can click the button “Start New Scan”.

1. Click the icon below to download the RegCure Pro.
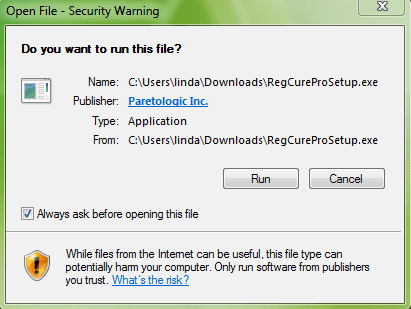
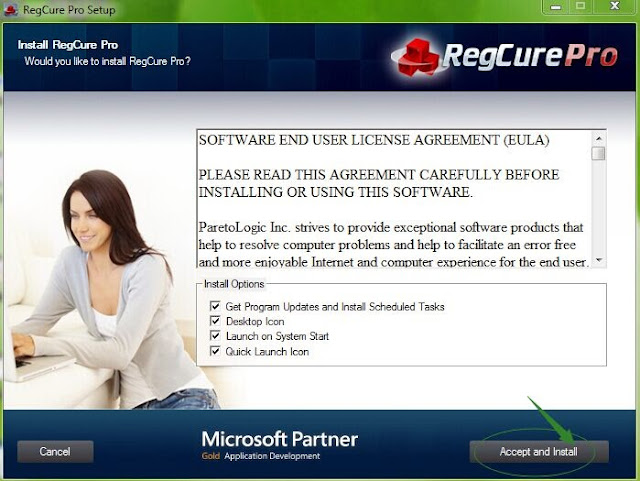
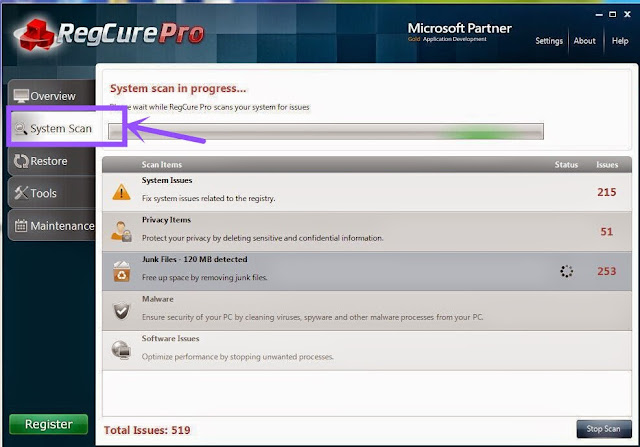
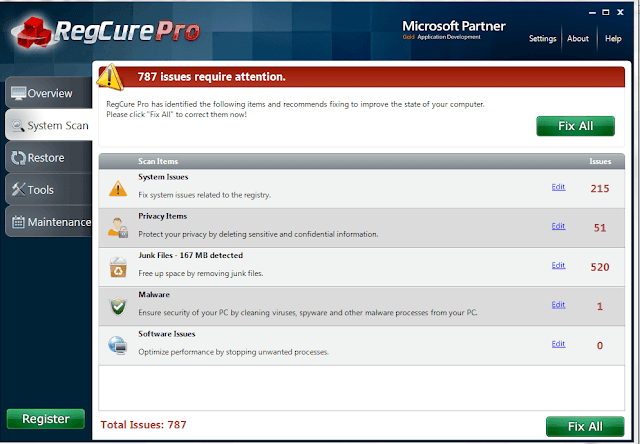
3. Click the button Accept and Install. And RegCure Pro will be installed successfully on your desktop. Then, open the RegCure Pro and it will start to scan your computer.
4. Click the button Fix All to optimize your PC.
If you want to safeguard your PC from malicious trojan virus, ransomware, malicious domain pop-ups, malware or other dangerous infections and keep your computer system in a safe condition, then you should take actions to protect your computer system appropriately and regularly. There are some tips recommended to you.
- Update your antivirus software regularly.
- Do not download and install freeware from unsafe sources.
- Do not open junk mails or suspicious email attachments.
- Dot not click on unknown links or ads from social networking sites easily.
- You should always scan the removable storage medium before using it.
- Make backups for your important files regularly.

No comments:
Post a Comment